How I discovered critical price manipulation
Hello Brothers,
I hope you have a nice day. Today I will share how I discovered price manipulation.
During my holiday, I started testing on a private program. The first thing I did was browse my target and try to discover the site’s features. After some time of browsing the target, I went to the payment page and started testing the payment functionality.
There are 3 payment plans, as shown below in the image.
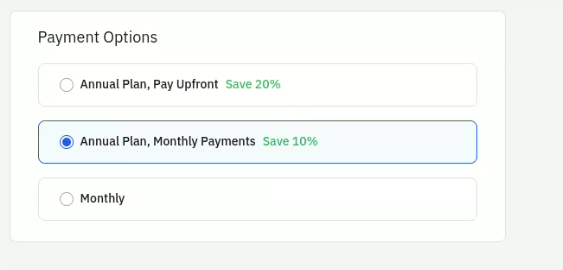
- Annual Plan, Pay upfront. This plan by default offers 20% off.
- Annual Plan, Monthly Payment. This plan by default offers 10% off, and the coupon that applied the 10% off exists in the URL.
- Monthly. This plan does not offer any discount.
Now we understand the 3 types of plans, let’s go to the exploitation.
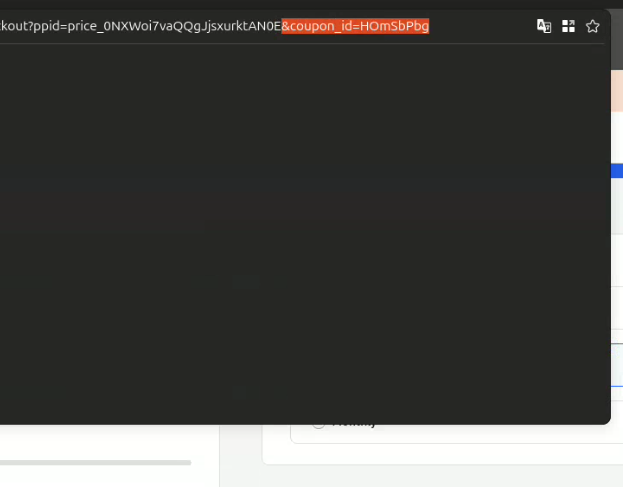
- First, I switched to the Annual Plan, Monthly Payment plan. I noticed that the coupon_id appears in the URL, as shown below.
After that, I switched back to the Annual Plan, Pay upfront plan and Fill all fields and clicked on next.
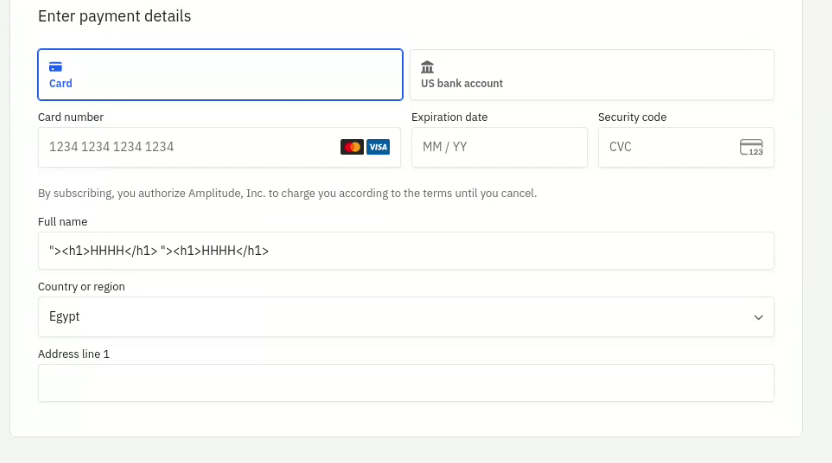
Then I added the Coupon_id parameter to the URL. I noticed that we can apply 30% off on this plan. By default, this plan allows only 20% off, but using this way I was able to apply 30% off, leading to more significant loss for the company.
Note: When I tried to use the Coupon_id parameter on an unauthorized plan, this didn’t work. But many times I noticed that we can use it on an unauthorized plan if we enter payment details and click on next , then append the Coupon_id to the URL. Otherwise, the PoC doesn’t work.
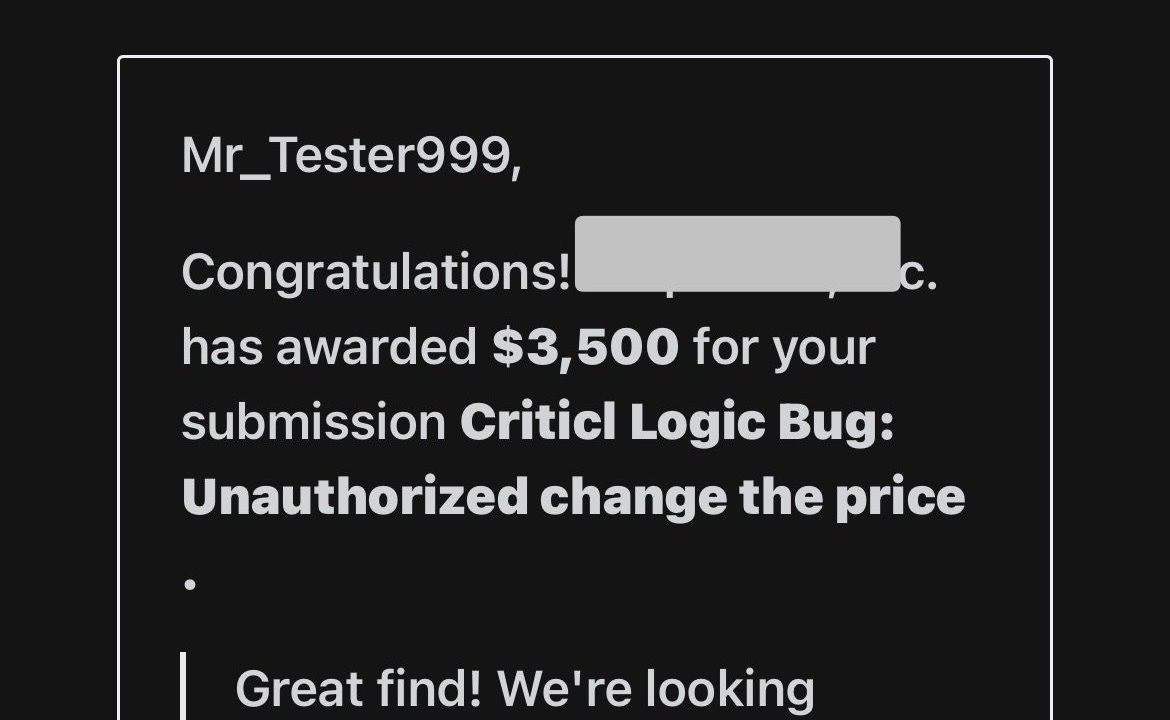
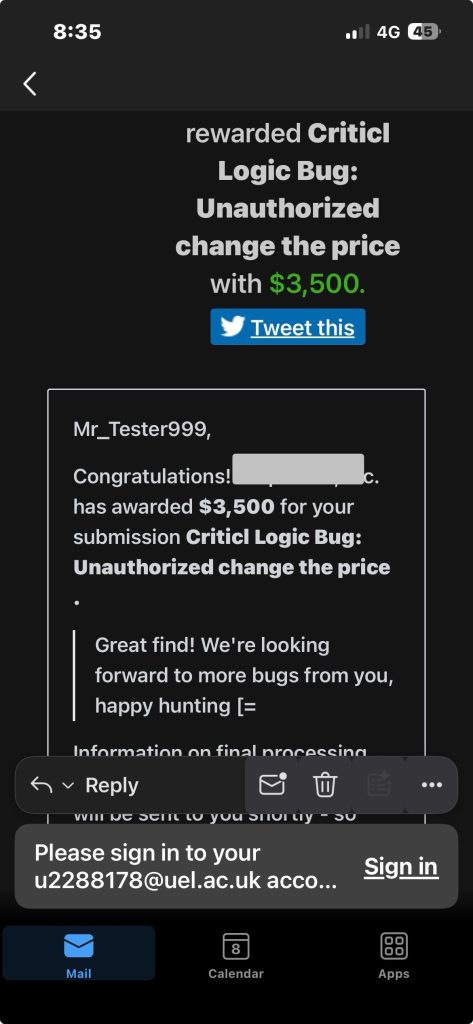
This is the response from the customer.
Unfortunately This reward is one of many rewards that I was not able to receive, due to my payment profile and my Bugcrowd account being blocked because of unintentionally breaking the payment policy.
Thank you, brothers. I hope this was useful for you. 👍
Leave a Reply